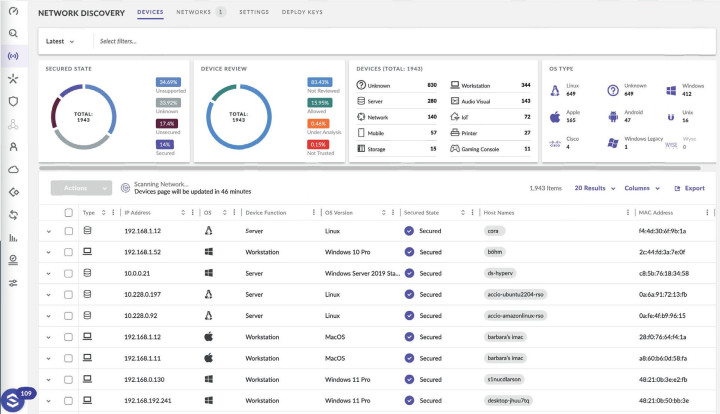
We support Windows, macOS, Linux, Android and IOS and cloud platforms AWS, Azure and Google.
A complete overview of connected computers with the possibility of remote management, installation of applications, running scripts, management of files and processes. The solution includes clear reporting.

Price is excluding VAT
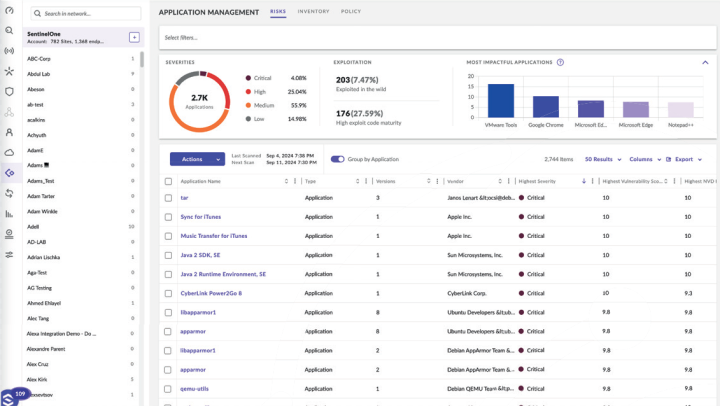
Application Inventory
Agent is protected against tampering
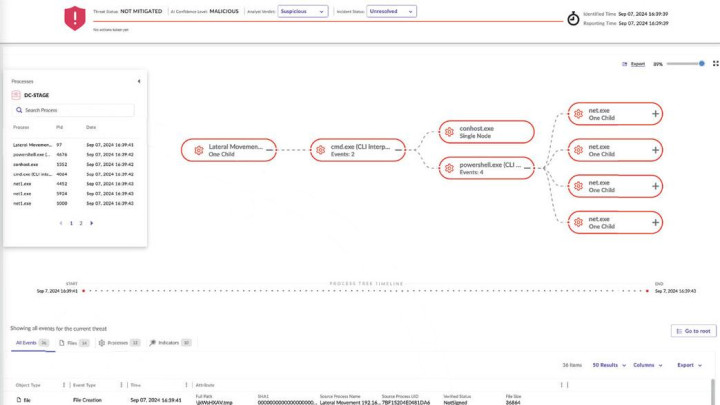
Incident Analysis (MITRE ATT&CK®, Timeline, Explorer, Team Annotations)
Device Quarantine from Network
Autonomous Rollback Response / 1-Click, No Scripting (Win)
Autonomous Remediation Response / 1-Click, No Scripting (Win, Mac)
Autonomous Threat Response / Kill, Quarantine (Win, Mac, Linux)
AI Fileless Behavioral Attack Detection
Static AI and SentinelOne Cloud File-Based Attack Protection
Sentinel Agent Storyline Standalone
Application Vulnerability (Win, Mac)
Rouge Device Discovery
Bluetooth / BLE Control (Win, Mac)
Location-Aware OS Firewall Control (Win, Mac, Linux)
Secure Re
Built-in static AI and behavioral AI analysis prevents and detects a wide range of attacks in real time before they cause damage. SentinelOne protects against known and unknown malware, Trojans, hacking tools, ransomware, memory abuse, script abuse, malicious macros, and more.